
The Sarbanes-Oxley (SOX) Act of 2002 was passed in the wake of several large accounting scandals at publicly traded companies. The goal of SOX is to improve corporate governance and accountability and ensure that financial reporting at all public companies is accurate. SOX hold executives directly responsible for the accuracy of disclosed financial information. The consequences for non-compliance can include steep personal fines and even jail time.
While SOX is applicable only to public companies, their financial data must be protected as mandated by SOX, even by any accounting firm or other third party that provides financial services to these public companies.
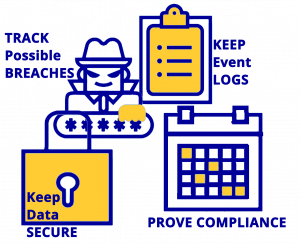
AlertSec provides a solid foundation for the implementation of internal controls that are mandated by SOX. AlertSec ensures the integrity of your customers’ financial data through encryption and by strictly managing user access to protected data. AlertSec also provides audit reports and activity tracking. This solid layer of technical security surrounding customer data is both highly effective and also unobtrusive to users, so it doesn’t affect normal business operations within your organization.
By minimizing the possibility of data breach or disclosure of information, AlertSec enables your organization to support your customers’ SOX compliance and SOX reporting requirements.
AlertSec Service features:
For many small to medium sized public companies, financial services partners may be contracted to handle financial data. Companies providing those financial services must be able to provide proof of their compliance with SOX with respect to protecting their partner’s financial data, just as the company does for the data it maintains in-house.
Unlike other regulations (such as HIPAA¹ or PCI-DSS²), SOX is not focused on the Confidentiality component of the information security triad: Confidentiality, Integrity and Availability. Instead, SOX compliance focuses on the Integrity of financial data. Data integrity relies on maintaining the security of the data in an auditable manner, so that company executives can be confident about the accuracy and reliability of the data disclosed in their financial reports. The internal controls that you implement to protect customer data will directly support your customers’ SOX compliance efforts and their confidence when partnering with you.
The best way to maintain the integrity of data is to protect the systems where data is accessed, keeping data transparently encrypted³ and also controlling who can access that data. AlertSec supports SOX compliance by providing a foundation of security and audit capabilities for your endpoint computers, creating a platform upon which you can build a complete compliance solution for your customers’ financial information.
The key is to be able to show how your overall security coverage enables your customers to be compliant, linking the security provided by internal controls to auditing so your customers can evaluate the reliability of the data by determining the security of your systems.
SOX does not define specific actions that must be undertaken to ensure compliance. Instead SOX defines the types of controls that need to be in place without specifying the details of how to implement them. This is both good and bad; it provides companies with the flexibility to implement controls that are appropriate for their size, choosing what will work best for them. Yet the flexibility potentially leaves a lot to interpretation by independent auditors.
To assist in building a complete “story” for your customers, you must be able to show how you have maintained their data in a compliant manner. The principle within SOX is that there are known internal controls and that these controls are well-established and auditable. By treating the controls required by SOX as if they were protecting your own data, you can assure customers about the quality of your compliance program when handling their financial data.
There are two sections of SOX that directly relate to information security:
Section 302 details the responsibilities of the signing officers with respect to the financial report. This includes the representation of accurate information, but also specifies that the officers implement, maintain and monitor internal controls to ensure the security and, by extension, the reliability of internal information.
Subsection 302.A.4 is about the responsibilities of the signing officers to establish the internal controls for protecting financial information. The internal controls that are implemented must be auditable and be able to generate reports that can be used to determine the effectiveness of these controls.
| Part | Description | Alertsec Support |
| A | Signing officers must establish and maintain internal controls | The AlertSec Service provides multiple modules to secure computers against many types of risk. |
| B | Internal controls must provide auditable events that can be reviewed | AlertSec provides audit records for all its services as part of the activity tracking that needs to be monitored |
| C | Internal controls must be reviewed (including audit records) within the 90 days prior to a report being issued to ensure the controls are functioning properly | AlertSec audit records and configuration settings can be reviewed at any time allowing an administrator to verify the operation of a device at any time |
| D | It must be possible to generate reports based on the internal controls that can be used to determine the effectiveness of said controls | AlertSec audit records are easy to read and can be exported in order to generate reports |
Subsection 302.A.5 is about establishing regular reviews of the internal controls to determine whether there are gaps in the coverage that could lead to unreliable data through the possibility of fraud or even the exposure of company financial data. Any issue with data integrity or fraud must be tracked and disclosed in an audit.
| Part | Description | Alertsec Support |
| A | Signing officers must report design deficiencies in the internal controls that could impact the reliability of financial data | AlertSec provides audit records detailing all protected systems and the status of that protection, pointing out gaps such as devices which have not installed the required software or have software that may be out of date |
Section 404 requires that an assessment of the internal controls must be performed and that a report of this assessment must be published as part of the financial report. The report must include the assignment of management responsibility for establishing and maintaining adequate internal control structures and procedures, and an assessment of the effectiveness of those controls.
| Part | Description | Alertsec Support |
| 2 | A report must be generated at the end of the fiscal year detailing the effectiveness of the internal controls, including gaps and breaches | AlertSec audit records and configuration settings can be reviewed at any time allowing an administrator to verify the operation and effectiveness of the protection on a device at any time |
| Description | Alertsec Support |
| The auditor must report on the assessment of the internal controls made by the officers | AlertSec audit records and configuration settings can be reviewed at any time to support a review of internal controls |
The AlertSec Service provides data protection as a service. Instead of requiring the purchase of several individual components and needing to manage them separately, the AlertSec Service provides a single, policy based, cloud-managed package of components that support your compliance requirements . The following modules and service features are available:
| Complance module | Description |
| Full Disk Encryption (FDE) | Automatic encryption for any digital personal or sensitive data on the computer. Ensures that only authorized users can access data on protected computers. AES-256 encryption for maximum protection, certification to FIPS 140-2, Common Criteria EAL4 and BITS. |
| Media Encryption/Port Control | Media Encryption automatically encrypts any personal data stored on removable storage media such as USB sticks and external hard drives based on policy. Data remains transparent to authorized users. Enables secure data sharing with other authorized users. Port control prevents use of unknown/unauthorized media on the computer, helping to prevent unsecure movement of personal or sensitive data. |
| Compliance Check | Scans and checks all endpoints for compliance with pre-defined security policies, enabling demonstration of security software deployment and management of software update installation compliance. |
| Anti-Malware/Program Control | Malware detection and prevention using signatures, behavior blockers and heuristic analysis. Policy controlled Program (application) Control can be configured to limit the applications that can be run on the system to only those that have been explicitly approved, helping to prevent threats to data integrity. |
| Firewall | Proactive policy based protection: the firewall blocks targeted attacks and stops unwanted traffic, keeping data and systems safe. |
| Encryption for third parties | Monitor and enforce full disk encryption policies across third party data processor service providers. Enables demonstration of security software deployment and management of software update installation compliance. |
| Two factor authentication for administrators | Additional security for privileged administrator accounts on the AlertSec admin console, helping to prevent unauthorized access or changes to security policies. |
| Pre-boot authentication | Ensures that only authorized users will be allowed access to personal or sensitive data stored on the device. Prevents anything being read from the hard disk, including the operating system, until the user has provided valid login credentials. |
| Password management | Automatic locking of a user account after five failed login attempts, preventing unauthorized access. AlertSec help-desk processes for password reset and data recovery are designed to ensure devices are unlocked only for the authorized user. |
| Software development and support | AlertSec manages the ongoing development and release of security software updates to maintain maximum protection. Regular customer communications about security risks and good practice enable employee training and security policy assessments. |
The high-level nature of the requirements specified in SOX gives you the flexibility to design a series of internal controls that best meets the needs of your organization and your customers when considering expertise, available resources and cost. AlertSec can play an important part in your SOX compliance solution by providing a baseline of security and audit capabilities that protect your customers’ financial information.
Implementing AlertSec FDE on the endpoint devices within the company ensures that any copies of customer financial data, such as offline copies for remote work, data in Word® documents or Excel® spread-sheets, or cached data from applications, are always secured on the endpoint device. AlertSec Media Encryption will enable you to securely utilize removable media to transport customer financial data between systems (such as when large volumes of data need to be backed up or delivered directly to another location, or where secure network transfers are not available or possible). AlertSec Port Control and Application control, combined with anti-malware protection, provide the ability to block access to removable media ports and block unwanted applications in order to prevent any customer financial data from accidentally leaking or being deliberately removed from the device.
By ensuring that the data is always encrypted and minimizing the possibility of unsecured access, you can provide assurance about the integrity of your customer’s financial data, while audit records ensure you can report on the status of your internal controls. With AlertSec you can ensure that your customers can meet the requirements for evaluating and reporting mandated by Sarbanes-Oxley.
The following selection of websites provide more information about SOX.
